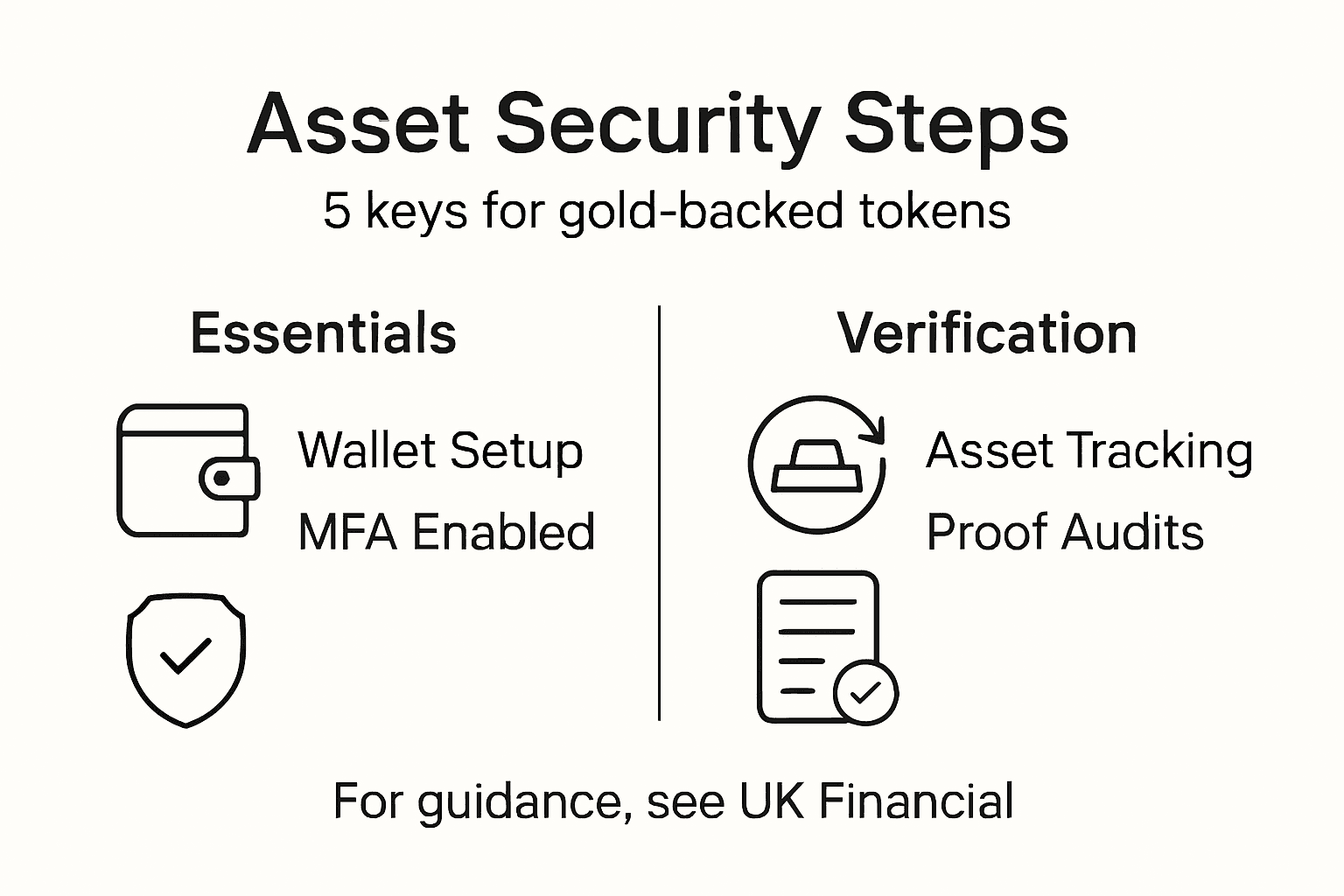
Step by Step Crypto Asset Security Guide for Gold-Backed Tokens

Managing significant digital assets calls for more than traditional security. With crypto investments directly linked to wealth preservation, institutional investors and wealth managers must now focus on robust protocols that blend secure storage, rigorous authentication, and transparent asset tracking. This guide highlights strategies for creating a secure, regulatory-compliant digital asset ecosystem backed by gold, offering practical steps to safeguard and verify holdings for long-term stability and portfolio diversification.
Table of Contents
- Step 1: Set up Secure Digital Wallets and Backup Methods
- Step 2: Implement Multi-Factor Authentication for All Accounts
- Step 3: Integrate Blockchain Asset Tracking and Proof of Reserves
- Step 4: Apply Regulatory-Compliant Storage and Access Controls
- Step 5: Verify Asset Security with Ongoing Audits and Performance Checks
Quick Summary
| Key Point | Explanation |
|---|---|
| 1. Secure your digital wallets effectively | Choose appropriate wallet types and security features to protect your cryptocurrency investments from theft and loss. |
| 2. Implement robust multi-factor authentication | Use multiple verification methods to enhance account security, making unauthorized access significantly harder. |
| 3. Utilize blockchain asset tracking | Leverage blockchain technology to maintain transparency and verifiability of your digital assets, improving trust and accountability. |
| 4. Ensure regulatory compliance in asset management | Establish comprehensive access controls and protocols that adhere to financial regulations for safe asset storage and management. |
| 5. Conduct regular audits for asset security | Continuous monitoring and systematic audits are essential for maintaining your assets’ integrity and identifying potential risks. |
Step 1: Set up secure digital wallets and backup methods
Protecting your digital assets requires strategic wallet setup and robust backup methods. This step will guide you through creating secure storage environments that shield your cryptocurrency investments from potential threats.
When establishing your digital wallet ecosystem, you’ll want to prioritize security by selecting the right wallet type. Cryptocurrency wallet security research reveals multiple wallet categories – including hot, cold, custodial, and non-custodial – each with unique security considerations. For institutional investors and serious wealth managers, we recommend a multi-layered approach:
- Cold storage wallets for long-term asset preservation
- Hardware wallets for substantial cryptocurrency holdings
- Multi-signature wallets that require multiple authentication points
Start by choosing a reputable wallet provider that offers advanced security features. Look for platforms providing:
- End-to-end encryption
- Offline storage capabilities
- Comprehensive backup and recovery mechanisms
- Two-factor authentication
Institutional-grade security isn’t just an option – it’s a necessity in the digital asset landscape.
Create your primary wallet using a dedicated device, preferably a hardware wallet like Ledger or Trezor. These devices store private keys offline, dramatically reducing hacking risks. When setting up, meticulously document and securely store your recovery phrases – typically a 12 or 24-word sequence that acts as your ultimate backup mechanism.

Here’s a concise comparison of cryptocurrency wallet types for institutional investors:
| Wallet Type | Security Level | Accessibility | Best Use Case |
|---|---|---|---|
| Hot Wallet | Moderate | High | Frequent trading |
| Cold Storage | Very High | Low | Long-term holding |
| Hardware Wallet | High | Medium | Significant asset protection |
| Multi-signature | Enhanced | Medium | Joint account management |
Backup Strategy Recommendations:
- Store recovery phrases in multiple secure physical locations
- Use fireproof and waterproof storage containers
- Consider split storage across geographically separate locations
- Never store recovery phrases digitally or in cloud services
Recommended Backup Tools:
- Titanium metal seed phrase storage
- Safety deposit boxes
- Personal safe with advanced security features
Pro tip: Consider creating a detailed backup protocol document that outlines your wallet recovery process, stored separately from your actual recovery information.
Step 2: Implement multi-factor authentication for all accounts
Securing your digital assets goes far beyond wallet setup – it requires a comprehensive approach to account protection that leaves no vulnerability unexposed. Implementing multi-factor authentication (MFA) creates critical layers of defense against unauthorized access.
Multi-factor authentication transforms your account security by requiring multiple verification methods before granting system entry. Typically, this involves combining something you know (password), something you have (mobile device), and something you are (biometric data). For institutional investors managing significant digital assets, this isn’t optional – it’s mandatory.
Authentication Methods to Implement:
- Hardware security keys
- Authenticator mobile applications
- Biometric verification
- SMS or email secondary codes
The weakest link in digital security is almost always human behavior, not technology.
When setting up MFA, choose authentication tools that provide robust encryption and verifiable security tracks. Look for platforms offering:
- Advanced encryption protocols
- Real-time breach detection
- Customizable security settings
- Comprehensive login history tracking
Your goal is creating a multi-layered authentication ecosystem that makes unauthorized access exponentially more difficult. Each additional authentication factor reduces compromise risks dramatically.
Best Practices for MFA Setup:
- Use dedicated devices for authentication
- Avoid SMS-based authentication when possible
- Regularly update authentication methods
- Monitor login attempts and locations
Recommended Authentication Tools:
- Google Authenticator
- Authy
- Yubikey hardware tokens
- LastPass Authenticator
Pro tip: Always maintain offline backup codes for your authentication methods in a secure, physically isolated location to prevent permanent lockout.
Step 3: Integrate blockchain asset tracking and proof of reserves
Ensuring transparency and verifiability of your digital assets requires implementing sophisticated blockchain tracking mechanisms. Cryptographic asset verification techniques provide institutional investors with powerful tools to validate token collateralization without compromising sensitive financial information.
Blockchain asset tracking represents a revolutionary approach to maintaining financial transparency. By leveraging advanced cryptographic protocols, you can create an immutable record of asset ownership, movement, and verification that provides unprecedented levels of trust and accountability.
Key Tracking Components:
- Real-time asset movement records
- Cryptographic verification protocols
- Transparent reserve validation
- Immutable transaction histories
Blockchain transparency isn’t just a feature – it’s a fundamental shift in financial trust mechanisms.
Implement your tracking strategy through these critical steps:
- Select a blockchain infrastructure compatible with your asset type
- Configure automated verification protocols
- Establish regular audit checkpoints
- Create comprehensive reporting mechanisms
Your goal is developing a comprehensive digital asset surveillance system that provides institutional-grade transparency. This involves integrating multiple verification layers that can independently confirm asset backing without revealing granular financial details.
Proof of Reserves Best Practices:
- Use zero-knowledge proof technologies
- Implement periodic independent audits
- Maintain cryptographic verification records
- Develop transparent reporting frameworks
Recommended Tracking Tools:
The following summarizes top blockchain asset tracking tools and their core strengths:
| Tool | Key Strength | Integration Potential |
|---|---|---|
| Chainlink Oracles | Reliable data feeds | Widely compatible |
| Merkle Tree Verification | Efficient asset proof | Scalable validation |
| Decentralized Audit Platforms | Independent review | Transparent reporting |
| Blockchain Explorers | Real-time analysis | User-friendly interface |
- Chainlink oracle networks
- Merkle tree verification systems
- Decentralized audit platforms
- Blockchain explorer technologies
Pro tip: Design your tracking infrastructure with modularity, allowing seamless updates and integrations as blockchain verification technologies continue evolving.
Step 4: Apply regulatory-compliant storage and access controls
Safeguarding your digital assets requires implementing robust, legally defensible storage and access management protocols. Establishing a comprehensive control framework protects your investments while ensuring alignment with global financial regulations.
Regulatory compliance isn’t just a checkbox – it’s a strategic approach to risk management that demands meticulous attention to detail. Your access control strategy must balance security, transparency, and operational flexibility while maintaining strict adherence to institutional standards.
Key Compliance Elements:
- Granular user permission systems
- Automated access logging
- Role-based security protocols
- Comprehensive audit trails
Compliance is not a destination – it’s an ongoing journey of vigilance and adaptation.
Implement your regulatory control strategy through these critical stages:
- Define precise user access hierarchies
- Create compartmentalized information zones
- Establish real-time monitoring mechanisms
- Design automatic compliance validation processes
Your objective is constructing a comprehensive regulatory defense infrastructure that anticipates potential vulnerabilities while providing seamless operational capabilities. This requires developing multi-layered access controls that can dynamically respond to evolving compliance requirements.
Access Control Best Practices:
- Implement zero-trust security models
- Use principle of least privilege
- Create adaptive authentication frameworks
- Maintain continuous compliance documentation
Recommended Compliance Tools:
- Identity management platforms
- Automated compliance tracking software
- Blockchain-based access control systems
- Advanced encryption key management solutions
Pro tip: Design your regulatory compliance framework with flexibility, anticipating future regulatory shifts while maintaining a consistent, auditable security posture.
Step 5: Verify asset security with ongoing audits and performance checks
Maintaining the integrity of your digital assets requires a proactive, systematic approach to security verification and performance monitoring. Your audit strategy serves as a critical defense mechanism against potential vulnerabilities and operational risks.
Ongoing asset verification is more than a compliance requirement – it’s a strategic imperative that provides real-time insights into your investment’s health and security posture. By implementing comprehensive audit protocols, you transform passive asset management into an active risk mitigation strategy.
Core Audit Elements:
- Automated security scanning
- Periodic penetration testing
- Continuous performance monitoring
- Cryptographic key rotation
Security is not a destination, but a continuous journey of vigilance and adaptation.
Execute your verification strategy through these systematic stages:
- Establish baseline security metrics
- Create automated monitoring dashboards
- Schedule regular comprehensive audits
- Develop rapid response protocols
Your objective is building a dynamic asset security verification ecosystem that provides instantaneous insights and immediate threat detection. This requires developing multilayered verification mechanisms that can seamlessly integrate technical assessments with strategic risk management.
Performance Audit Best Practices:
- Implement zero-trust verification models
- Use machine learning anomaly detection
- Maintain detailed audit trail documentation
- Conduct quarterly comprehensive reviews
Recommended Verification Tools:
- Advanced blockchain explorers
- Cybersecurity monitoring platforms
- Automated compliance tracking software
- Cryptographic validation systems
Pro tip: Design your verification infrastructure with built-in adaptability, ensuring your audit mechanisms can evolve alongside emerging security technologies and threat landscapes.
Secure Your Investment in Gold-Backed Crypto Assets Today
The step-by-step guide highlights critical challenges like creating multi-factor authentication, implementing blockchain asset tracking, and ensuring regulatory-compliant access controls to safeguard your digital wealth. These pain points require a partner who prioritizes transparency, proof of reserves, and robust security protocols to protect your gold-backed tokens from evolving risks.
At UK Financial Ltd, we understand that institutional and retail investors demand confidence in the authenticity and safety of their precious metal–backed cryptocurrencies. Our platform offers real-time blockchain tracking, comprehensive proof of reserve reports, and a secure ecosystem designed to meet strict compliance standards. This allows you to confidently preserve and diversify your portfolio with tokens like Maya Preferred PRA and MayaCat meme coin.

Take control of your asset security with our verified gold-backed tokens and transparent governance. Visit UK Financial Ltd now to explore how we make blockchain asset security accessible and dependable. Learn more about our portfolio of tokens and start your secure investment journey without delay.
Frequently Asked Questions
How do I set up a secure wallet for my gold-backed tokens?
To set up a secure wallet for your gold-backed tokens, choose a reputable wallet provider and create a hardware wallet for best security. Document your recovery phrases carefully, store them in secure locations, and ensure regular backups to mitigate loss risks.
What types of authentication should I use for my crypto accounts?
Implement multi-factor authentication (MFA) that includes both hardware security keys and mobile authenticator apps. This adds an additional layer of security by requiring more than just your password for account access, significantly reducing the risk of unauthorized entry.
How can I track my gold-backed tokens securely on the blockchain?
To track your gold-backed tokens securely, integrate blockchain asset tracking tools that provide instant verification of ownership and transaction histories. Implement real-time monitoring and establish audit checkpoints to ensure asset integrity and transparency.
What measures should I take to ensure compliance with cryptocurrency regulations?
To ensure compliance with cryptocurrency regulations, implement granular user permission systems and maintain detailed access logs. Regularly review your compliance protocols and adapt them to evolving regulations to safeguard your assets legally.
How often should I conduct audits of my digital assets?
Conduct audits of your digital assets at least quarterly to maintain security and verify asset integrity. Establish automated monitoring systems to track performance continuously and detect any anomalies promptly.
What should I include in my backup strategy for gold-backed tokens?
Your backup strategy should include securely storing recovery phrases in multiple physical locations and using fireproof containers. Additionally, maintain an easily accessible recovery protocol document that outlines procedures for asset recovery in case of emergencies.
Recommended
- UK Financial Ltd – Gold-Backed Cryptocurrency Portfolio
- UK Financial Ltd Receives Recognition In Platinum Crypto Academy’s Cryptonaire Weekly
- UK Financial Ltd Announces CoinMarketCap Supply Verification And Market Positioning Review For Regulated Security Tokens SMPRA And SMCAT
- UK Financial Ltd Establishes United States Operations in Delaware, Announces Texas Expansion
- Top 5 Investiciono-zlato.com Alternativa 2026 za Individualne Investitore i Kolekcionare Zlata